Protecting Your Crypto Treasure: The Hidden Price of Neglecting Privacy

In an era where the digital landscape evolves rapidly, ensuring your online privacy is paramount. This rings especially true in the realm of cryptocurrencies, where safeguarding your assets is contingent upon securing your personal information. In this article, we’ll explore the growing importance of privacy protection and delve into the various threats that emanate from data breaches, all while weaving in real-life examples to underscore these concerns. Additionally, we’ll discuss the different facets of data protection and the tactics employed by cybercriminals to target and blackmail unsuspecting victims.
Privacy Protection: More Crucial Than Ever
The Recklessness and Indulgence
Unfortunately, many individuals inadvertently contribute to their own vulnerability by sharing an excess of personal information online. Overindulgence in social media, oversharing personal details, and neglecting cybersecurity measures can lead to dire repercussions. It’s crucial to recognize that every piece of information you divulge online can potentially be used against you, particularly in the context of cryptocurrency assets.
The Multifaceted Arena of Data Protection
Securing your data encompasses various aspects, spanning from safeguarding private messages and protecting local drives to securing cloud storage and safeguarding personal information, such as family details, job-related data, and social status. Each element presents a potential entry point for cybercriminals seeking to exploit unsuspecting victims.
Cybercriminal Tactics: A Persistent Threat
Cybercriminals are relentless in their pursuit of lucrative targets, such as individuals with substantial cryptocurrency holdings. They employ an arsenal of tools and methods to catch victims off guard. For example, they may attempt to physically locate their target by leveraging the victim’s cryptocurrency transactions to map their location. Additionally, they employ social engineering tactics, such as creating enticing websites or employing phishing schemes to collect IPs and other sensitive data.
Border Searches
Border searches of electronic devices have been on the rise, raising concerns about travellers’ digital privacy. With the increasing amount of highly personal information stored on our phones, laptops, and other electronic devices, including private emails, text messages, photos, and more, it’s crucial to understand how to protect your digital data. While the U.S. Constitution places limits on government intrusion into our private lives, the so-called “border search exception” allows warrantless searches at the border, with the assumption that travellers have limited privacy interests in their belongings.
This topic is so broad that we recommend referring to the Electronic Frontier Foundation (EFF), which actively works to address it. To learn more about safeguarding your digital privacy at the border, you can explore EFF’s comprehensive travel guide, their research on border agency device searches, and their legal work and advocacy efforts.
Real-Life Examples of Privacy Breaches
The Menace of Data Breaches
The digital landscape is replete with instances of data breaches that have led to devastating consequences for individuals and organizations alike. Consider the case of Equifax, a credit reporting agency that suffered a massive breach in 2017, exposing the personal information of nearly 147 million people. Cybercriminals leveraged this stolen data to commit identity theft and financial fraud, wreaking havoc in the lives of countless individuals.
The Tale of Joe: A Cautionary Tale
Consider “Joe,” who received a phone call from an individual posing as a Binance employee. The imposter was astoundingly convincing and well-versed in the art of impersonation. Joe, taken aback by the sudden call, quickly realized the gravity of the situation as the imposter urged him to act swiftly to protect his assets. Joe, displaying prudence, asked a crucial question:
“- How can I be sure you’re really calling from Binance?”
Armed with personal information obtained through a prior data breach, the imposter sought to allay Joe’s doubts. However, Joe’s instincts kicked in, and he redialed the number, only to be greeted by a different voice and background noise.
Scam Alert: It turns out that the GSM network has several easy-to-exploit vulnerabilities. The one described here is known as “phone spoofing,” where the attacker uses a simple modem connected to a regular mobile phone. This modem allows a malicious actor to input virtually any phone number to be displayed as the ‘caller ID.’ By doing this, they not only conceal the real number they used to make the phone call, but they can also go a step further and impersonate an institution or even someone whose phone number you have saved in your address book!
This incident underscores the importance of remaining vigilant in the face of unexpected calls or messages.
In Joe’s case, the chain of events traced back to his purchase of a Bitcoin-related book from an online store with subpar data security measures. The breach of this store’s data led to the exposure of Joe’s interests in cryptocurrencies. Cybercriminals, armed with this information, attempted to manipulate him using urgency and fear, but Joe’s caution saved the day.
CRYPTO TOOLBOX
Pragmatic Approach To Preserve Your Privacy
In the dynamic world of online privacy, adopting a pragmatic approach is crucial to thwart potential threats effectively. Here, we will delve deeper into strategies to safeguard your personal information while enhancing your digital security.
Disposable Email Addresses as a Shield
One formidable strategy is the use of disposable email addresses. In the event of an unexpected call or message, verifying the caller’s knowledge of your email address can serve as a litmus test for their authenticity. Cybercriminals, armed with stolen data, may attempt to bluff their way through, but your vigilance will be your greatest asset.
Moreover, services like SimpleLogin, or Norton Antitrack offer a seamless solution. They enable you to manage multiple disposable email addresses through a single inbox while keeping your real email address concealed. This ingenious approach not only adds an extra layer of security but also streamlines your digital communications, making it a practical choice in today’s data-sensitive landscape.
Hint: The premium plan of Proton Suite comes already with SimpleLogin!
Obscuring Your Digital Footprint with VPNs
Cybercriminals, driven by the allure of substantial cryptocurrency holdings, may resort to physical visits based on geolocation data obtained from various sources. Protecting your physical safety is paramount, and a Virtual Private Network (VPN), or Decentralized Private Network (DPN) can help obscure your real IP address. By routing your internet traffic through secure servers located worldwide, or secure multiple peer-to-peer nodes, they make it impossible for malicious actors to pinpoint your exact location, bolstering your defense against physical threats.
Guarding Against the "Man-in-the-Middle" Exploits
Public Wi-Fi networks, often found in coffee shops, airports, and malls, present a convenient way to connect to the Internet while on the go. However, they are also prime targets for “Man-in-the-Middle” attacks. In such scenarios, cybercriminals intercept communication between your device and the internet, potentially leading to data breaches and compromises.
To safeguard your digital integrity, exercise caution when connecting to public Wi-Fi networks. Consider using a reputable VPN or DPN service, which encrypts your data and shields it from prying eyes. This proactive step ensures that even on public networks, your online activities remain confidential and secure.
Beware of Malicious Links and Manipulative Tactics
Social engineering remains a potent weapon in the arsenal of cybercriminals. They capitalize on human psychology to manipulate unsuspecting individuals into divulging sensitive information or engaging in actions that compromise their security.
Social engineering can take many forms, including unsolicited messages or emails that appear trustworthy. A seemingly friendly message from an unknown source may entice you to click on a link or share personal details. This seemingly innocuous action can lead to the revelation of your IP address or even your wallet address, putting your assets at risk.
In the cryptocurrency realm, it’s crucial never to share your secret recovery phrase, also known as Seed Words, with anyone. No legitimate entity or individual needs this information to assist you. While this advice may seem repetitive, its importance cannot be overstated. The security of your cryptocurrency holdings hinges on your discretion in guarding this critical information.
We discuss this type of phishing (among many others) in our blog post.
The Pitfalls of Overconfidence And The Unintended Exposure
In your pursuit of cryptocurrency investments, it’s easy to become overconfident, especially when sharing your success with trusted acquaintances. However, even among friends and family, exercising discretion is paramount.
Amid the camaraderie of family gatherings or social events, you may be tempted to discuss your cryptocurrency holdings. However, doing so inadvertently exposes you to potential threats. Cryptocurrency investments should be treated with the same discretion as traditional financial matters.
Your friends and family, no matter how trustworthy, may inadvertently reveal your financial status to others or become targets themselves. It’s essential to strike a balance between sharing your successes and safeguarding your financial assets. Vigilance, even among those closest to you, is a vital element of maintaining your online privacy and financial security.
Did You Know That You Can Learn A Safe Way To Generate Passive Yield With Your Crypto Over The Next Decade?
Unlock the power of digital assets with HEX Passive Income. This course takes you from novice to pro in the world of cryptocurrency investments in just a few weeks. Learn the secrets of yield farming, PulseChain staking, and the HEX staking ladder system. Get started today for financial freedom.
Additional Steps for Protecting Your Cryptocurrency
Implementing Two-Factor Authentication (2FA)
In addition to the strategies mentioned earlier, consider implementing Two-Factor Authentication (2FA) for your cryptocurrency accounts. 2FA provides an additional layer of security by requiring you to provide a second piece of information, such as a one-time code from an authentication app, in addition to your password. This extra step can thwart unauthorized access even if your password is compromised.
Secure Hardware Wallets
For added security, explore the use of hardware wallets to store your cryptocurrency. These physical devices are designed to keep your private keys offline, making it extremely difficult for hackers to gain access to your assets.
Community Vigilance
Stay engaged with the cryptocurrency community to stay informed about the latest threats and scams. Sharing your experiences and learning from others can be a valuable part of your security strategy.
Solid Education
Continuously educate yourself about cryptocurrencies and online security. Staying informed about the latest developments is essential for adapting to new threats.
Create an Emergency Plan
Prepare for the worst-case scenario, such as a catastrophic hardware failure. Have a plan in place for recovering your assets or passing them on to trusted individuals.
Did You Hear About Our Free E-Book?
There’s much more to becoming successful in crypto, but safeguarding your digital assets is a substantial part. Best of all, it doesn’t have to be complicated. Sign up for our powerful newsletter to enhance your crypto skills right now!
Conclusion
In conclusion, the world of cryptocurrency demands vigilance and an unwavering commitment to online privacy. The strategies outlined here offer a comprehensive approach to safeguarding your personal information and digital security. By adopting a pragmatic stance, obscuring your digital footprint, and remaining vigilant against social engineering and overconfidence, you can fortify your digital fortress in an ever-evolving landscape of cyber threats. In the cryptocurrency age, protecting your assets begins with protecting yourself. Stay safe, stay private, and protect your digital wealth.
Recommended Tools for This Article
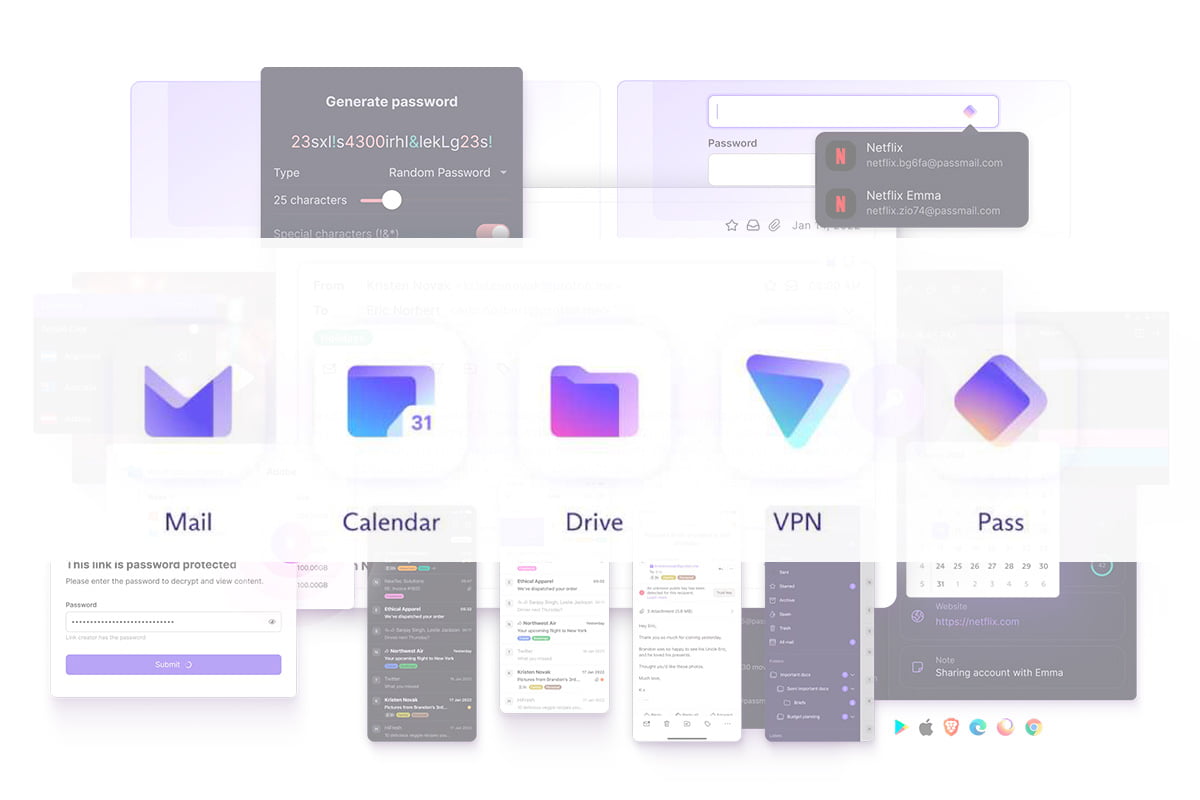
PRIVACYPROTON APPS | State-Of-The-Art Privacy Management Suite (incl. Webmail, Password Manager, Drive, VPN, and Calendar)
Proton is a Swiss-Based company that delivers the industry top-level tools to ensure your information is always yours and no one else can read it. As their slogan says "Privacy By Default" - there is much more to it. Sign-up for a free account and check by yourself.
SECURITYDEEPER CONNECT | Decentralized VPN With a 7-Layer Firewall & Enterprise-Grade Security, Offers Unparalleled Protection. No Monthly Fees.
Decentralized Private Network (DPN) is a technology that offers enhanced privacy and security for your internet connection. Unlike traditional centralized VPNs, DPN operates in a peer-to-peer manner, which makes it more secure and private. With DPN, you connect to other nodes or devices instead of a centralized server. This decentralization also makes DPN resistant to censorship, ensuring access to information even in regions with strict online restrictions.
SECURITYTREZOR | Most Secure And Time-Proven Hardware Wallet
Grab your Trezor device, plug it in, open Trezor Suite, and let your crypto journey begin. Let The Trezor Hardware Wallet Shield Your Digital Assets Now!






 Don't Let Scammers Win! Discover The Ultimate Defence Strategies For Your Digital Wealth & Secure Your Crypto Future - Now!
Don't Let Scammers Win! Discover The Ultimate Defence Strategies For Your Digital Wealth & Secure Your Crypto Future - Now!